Generating a valid self-signed certificate for Apache and Chrome
Certificate generation
Assuming that you are on Windows, you have installed OpenSSL in C:\OpenSSL-Win32\ and your local domain name is nullalo.local, you can issue the following commands at the prompt:
C:\OpenSSL-Win32\bin\openssl.exe req -x509 -config C:\OpenSSL-Win32\bin\openssl.cfg -nodes -days 365 -newkey rsa:2048 -reqexts SAN -extensions SAN -keyout nullalo.local.key -out nullalo.local.crt
Let’s see the meaning of this command’s parameters:
- x509 is the certificate standard (X.509 v3)
- nodes stands for “No DES”, meaning your private key will not be encrypted in a PKCS#12 file with 3DES-CBC algorithm
- days is the number of days of validity from the current date (in the example, 365 days – 1 year from now)
- newkey generates a new RSA key of ‘bits’ in size (in the example, 2048 bits)
- reqexts specifies request extension section (in our case, SAN – override value in config file)
- extensions specifies certificate extension section (SAN, again – override value in config file)
- keyout outputs private key to a file
- out outputs certificate to a file
You’ll be asked for some informations about the certificate: it is very important, for previous Google Chrome version and other browsers, that when asked for Common Name, you enter your primary DNS (in this case, nullalo.local).
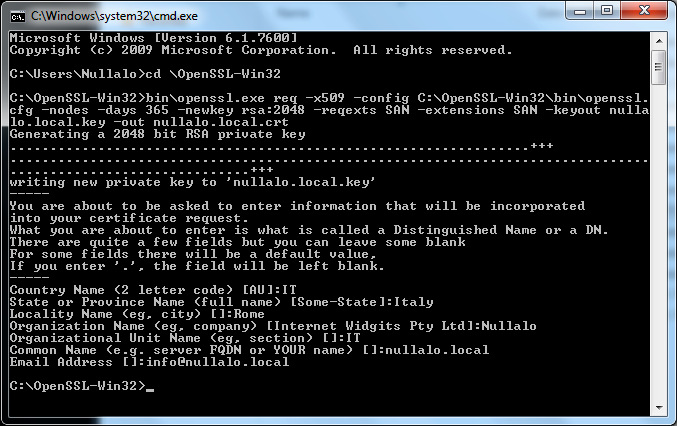
This command will generate, in the current directory, two files: the private key (nullalo.local.key) and the self-signed certificate (nullalo.local.crt).







4 Comments
Thanks a ton!!
This tutorial worked for me perfectly.
Davvero interessante 🙂 Grazie
Hi,
I install SELF-SIGNED CERTIFICATE on my site http://www.nspiel.de/ , and check on ssllabs.com it said: NOT TRUSTED.
What can I do now?
This procedure is for LOCAL certificates. For an online website, you have to use Let’s Encrypt or something similar, but in the meanwhile I see you already solved your issue 🙂